Nowadays, there is a lot of talk about security culture and how we can make organizations embrace and build it. But how does one go about building a security culture? How can it be measured, improved or changed?
In many cases, organizations are approaching security culture wrong. One of the main reasons for this is that they approach a culture change program the same way they would roll out a strategic change.
Allow me to illustrate with an example.
Most of us are familiar with Martin Luther King Jr.’s infamous phrase, “I have a dream.” This is an example of someone who understood that a cultural change was needed, and to facilitate that change, he needed to appeal to people’s emotions. He needed to share a vision of hopes and dreams. Consider if he made the same speech, but instead of saying he had a dream, he started off by saying he had a seven-point strategic plan on how to achieve equality. The message may have been the same, but it would have been received very differently.
Changing the security culture of an organization is not something that can be easily captured within a single blog post. It would likely take a book (or two) to fully flesh out the ideas and concepts.
But for those looking to embark on a culture change program, the following three pillars can serve as a good foundation to start from:
Understand What Needs to Change
Before diving headlong into a culture change program, it is essential to understand what aspects of culture need to be changed. It’s easy to say that an organization needs a security culture, but which behaviors does that translate into?  Before diving headlong into a culture change program, it is essential to understand what aspects of culture need to be changed.Courtesy of Getty Images — Credit: Prostock-Studio
Before diving headlong into a culture change program, it is essential to understand what aspects of culture need to be changed.Courtesy of Getty Images — Credit: Prostock-Studio
A good way to go about this is to have small workshops with people across different departments and follow this four-step process to identify some ideas:
What cultural behaviors are we trying to change?
Turn that problem into a question.
What challenges are there?
List out some solutions. A simple example of an organization working through these steps could look like this.
People don’t lock machines when walking away from them.
How can we encourage people to lock their machines when walking away from them?
People don’t know how to lock their machines.
They think it’s safe.
They don’t like re-entering their password when they return.
Add stickers to the keyboards to remind people how easy it is to lock their machines.
Set up a screensaver to lock the machine after 30 seconds of inactivity.
Use proximity cards to automatically lock the machine when the user walks away.
Penalize users of unlocked machines.
Enable fingerprint readers for quick logon.
Once a number of solutions have been proposed, one can plot them in an effort vs impact chart to see which ones are worth pursuing. Ideally, you want to look for low effort and high impact ideas that can reduce the burden of a task from a user while nudging them to do the right thing. 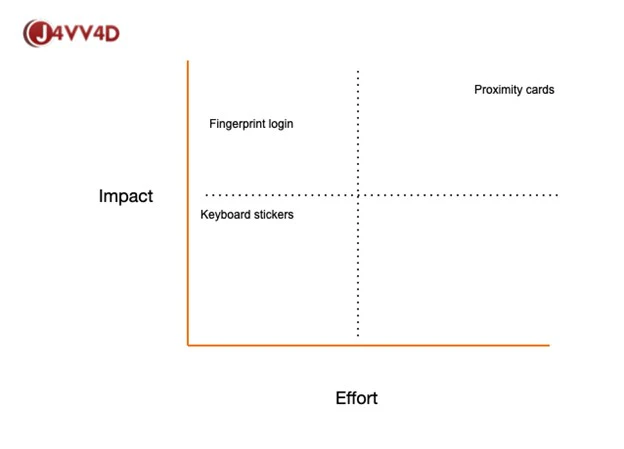
In the simple example, our imaginary focus group came to the consensus that while proximity cards may have the greatest impact, they did require the greatest effort (cost, time, resources).
However, enabling fingerprint logins and having stickers on the keyboard to remind people to hit them when walking away would be the easiest to implement.
Focusing Efforts
So, now we have a way forward – we realize that part of the culture change in our fictitious and simplistic organization is to have people lock their machines when they leave them unattended.
But a mistake that organizations make is that they try to roll out the solutions to the entire organization, and that doesn’t always work. In order to better understand how to change the hearts and minds of people, we have to go back in time to 1962 and refer to Everett Rogers who first proposed the law of diffusion of innovation. 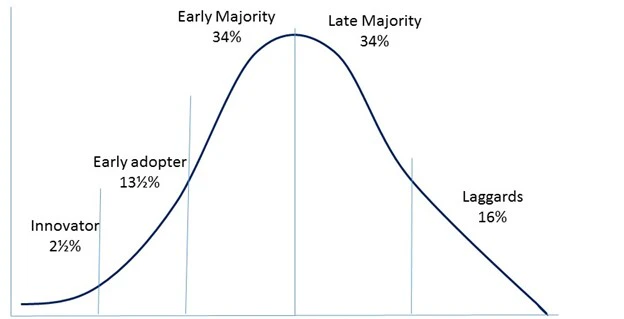
You may look at this and think that it is just a bell curve. And you’d be right to think that. But this bell curve applies to many things related to purchasing decisions and our case behavior change. Common sense would dictate that in order to popularize an idea, we should target the early and late majority groups. Once the majority has adopted a behavior, value or product, then that will influence the entire culture.
However, the majorities are suspicious of change – and in many ways, are practical people. Why should they adopt a new practice that has no visible benefit to them, or that takes up time and effort?
So, in reality, you need to target the early adopters – and only the early adopters.
Who Are the Early Adopters?
Early adopters are those who will stand in line all night just to buy the latest technology or watch a movie on release night. They know all too well that if they wait a week, they could simply walk into the shop or the theatre and avoid the hassle. But it is that hassle that drives an early adopter – they are so intent on being the first and experiencing something before others that they will ignore the pain. They see the end goal before others and are willing to adopt it before others.
More importantly, early adopters don’t just experience something first, they are then more than happy to share their experiences with others.
In a security context, we can refer to these people as “culture carriers.” Some organizations refer to these people as security ambassadors or evangelists. The term is not important; what is important is that these people have social connections that allow them to spread ideas to a vast amount of people in a short period of time.
Usually, they are connected in many different areas, so the ideas spread outside of traditional silos.
Tipping Point
Once enough culture carriers have been established, the job is to keep the momentum going until it reaches the tipping point and spills into the majority.
What that means is that you help keep the culture carriers highly engaged and enable them to share their message and tips on why locking workstations when leaving them unattended is a great thing to do.
Malcolm Gladwell, in his book, “Tipping Point,” articulates three rules that contribute to a tipping point where an idea becomes viral.
- The Law of the Few
Based on the well-known “Pareto Principle,” or “80/20 Principle,” the Law of the Few states that the most significant attention will come from only a few key players. As the Pareto Principle states it, 80% of the action will be driven by 20% of participants. The Law of the Few also discusses that these key players have specific roles. “Mavens” are the information specialists, “connectors” or carriers are those who bring the idea to larger networks of consumers, and “salesmen” are those who, well… sell it! You can also think of these key players as the early adopters of the innovation or idea.
- The Stickiness Factor
This essentially asks how memorable an idea, product or service is and how easily it can catch on among consumers and participants. In his book, Gladwell uses popular children’s shows like “Blue’s Clues” and “Sesame Street” to show how they pioneered a new, sticky way for children to learn, which enhanced retention and entertainment value.
- The Power of Context
This rule is based on the concept that human behavior has strong ties and sensitivity to its environment. When ideas and innovative concepts are introduced with key timing and placement, the strong context can be an added boost in dissemination.
Intensity vs. Consistency
By now you have your plan, you’ve identified your early adopters, and you have them socializing the right cultural values to the masses. It is at this point where many organizations let their foot off the gas. After all, it is a case of ‘mission accomplished’… right?
You see, cultural change in an organization requires a lot of individual behaviors to change – and this does not happen overnight. It may occur for a short period of time, like how a diet survives a few weeks into January before losing momentum.
It is why organizations need to plan their strategy around consistency – it’s a marathon, not a sprint. Many organizations fall into the trap of trying to change security culture through intense bursts – new initiatives are released, re-orgs are undertaken, and turnaround consultants are air-dropped in. But that’s not what changes a culture – at most, it merely suppresses the real culture until the pressure subsides and people return to normal again.
Consider a close friend. At one time you were strangers, but over time you became friends. There wasn’t a definitive moment in time where you suddenly thought you needed to move that person from acquaintance to friend category. It was something that happened over a long period of time. Meeting up, sharing experiences, buying each other coffee, remembering details about them, and so on. As an individual action, having a coffee with someone doesn’t make them your friend. But repeat the process over a period of time, get to know how they like it, share hours of conversations, and maybe it will happen.
Culture change within an organization can be much the same.
Measure
By this stage, you’ve identified the behaviors that need to change within the organization to affect the culture. You’ve identified your early adopters, and put a consistent plan in place in order to reach the tipping point to shift the culture to a more secure one.
But how do you measure the change? Are you even making an impact or are you merely spending resources on a mission that may not be working?
This is where an objective scientific method for assessing, reporting and comparing security culture is necessary. Fortunately, better minds than mine have applied a lot of thought to this. Cltre (a KnowBe4 company) sets out how security culture can be systematically evaluated across seven distinct dimensions. 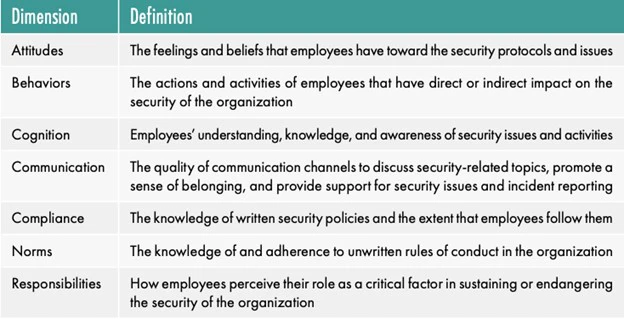
Using a methodology that can help organizations consistently and reliably measure what impact their efforts are having on security culture and use the information to make informed decisions about what tactics to adopt going forward.
Parting Thoughts
All too often, organizations see cultural initiatives as a last resort. Often, culture is looked at as a way to blame an organization’s resistance to major change-making culture a scapegoat as opposed to something that can empower organizations.
Security culture needs to be defined in a way that makes it easy to understand, easy to measure and easy to manage. By defining security culture as the ideas, customs and social behaviors of an organization that influence their security, it becomes clear that security culture is closely linked to culture at large. To work with culture, we must first understand it. It should be clear that to measure and manage culture, we need to apply other tools, techniques and practices than traditional security controls.
About the Author: Javvad Malik is a Security Awareness Advocate at KnowBe4, provider of the world’s largest security awareness training and simulated phishing platform.  Javvad Malik is a Security Awareness Advocate at KnowBe4, provider of the world’s largest security awareness training and simulated phishing platform.Prior to joining KnowBe4, Javvad was a security advocate at AlienVault. Before then, he was a Senior Analyst at 451’s Enterprise Security Practice (ESP), providing in-depth, timely perspective on the state of enterprise security and emerging trends in addition to competitive research, new product and go-to-market positioning, investment due diligence and M&A strategy to technology vendors, private equity firms, venture capitalists and end-users. Prior to joining 451 Research, he was an independent security consultant, with a career spanning 12+ years working for some of the largest companies across the financial and energy sectors. As well as being an author and co-author on several books, Javvad was one of the co-founders of the Security B-Sides London conference.
Javvad Malik is a Security Awareness Advocate at KnowBe4, provider of the world’s largest security awareness training and simulated phishing platform.Prior to joining KnowBe4, Javvad was a security advocate at AlienVault. Before then, he was a Senior Analyst at 451’s Enterprise Security Practice (ESP), providing in-depth, timely perspective on the state of enterprise security and emerging trends in addition to competitive research, new product and go-to-market positioning, investment due diligence and M&A strategy to technology vendors, private equity firms, venture capitalists and end-users. Prior to joining 451 Research, he was an independent security consultant, with a career spanning 12+ years working for some of the largest companies across the financial and energy sectors. As well as being an author and co-author on several books, Javvad was one of the co-founders of the Security B-Sides London conference.



